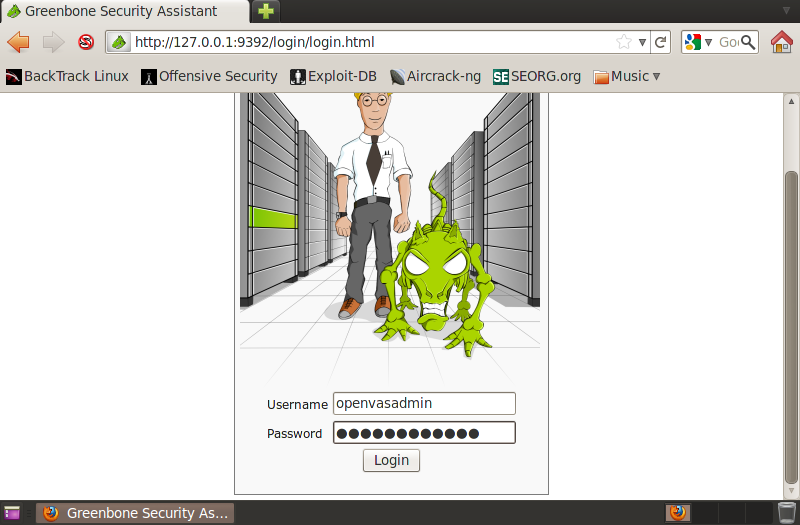
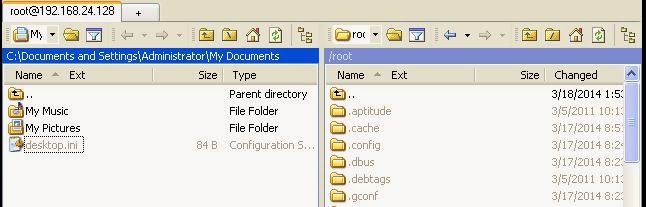
How to Install and Configure OpenVAS: Setup guide
OpenVAS stands for Open Vulnerability Assessment System. It is the collection of several tools and services which offers vulnerability scanning and management solution. OpenVAS is free and it is licensed under GPL (GNU General Public License). Lets start with the step by step guide on installing and configuring the OpenVAS in linux machine. Here we … Read more